Introduction:
Access control credentials are an essential part of modern security systems.
They provide an effective way to restrict access to sensitive areas, information, or assets.
Access control credentials are a type of authentication mechanism that is used to verify an individual’s identity and grant access to restricted areas. In this article, we’ll take a closer look at what access control credentials are, how they work, and why they’re important.
What Are Access Control Credentials?
Access control credentials are unique identifiers that are used to grant or deny access to a specific area or resource.
These credentials can be in the form of a physical card, a key fob, vritual card or a digital token.
Access control credentials typically contain information about the user, such as their name, ID number, or other identifying details.
The credentials are verified by an access control system, which checks them against a database of authorized users. If the credentials are valid, the user is granted access; if they’re not, the user is denied access.

Types of Access Control Credentials:
There are several types of access control credentials that are commonly used in security systems. These include:
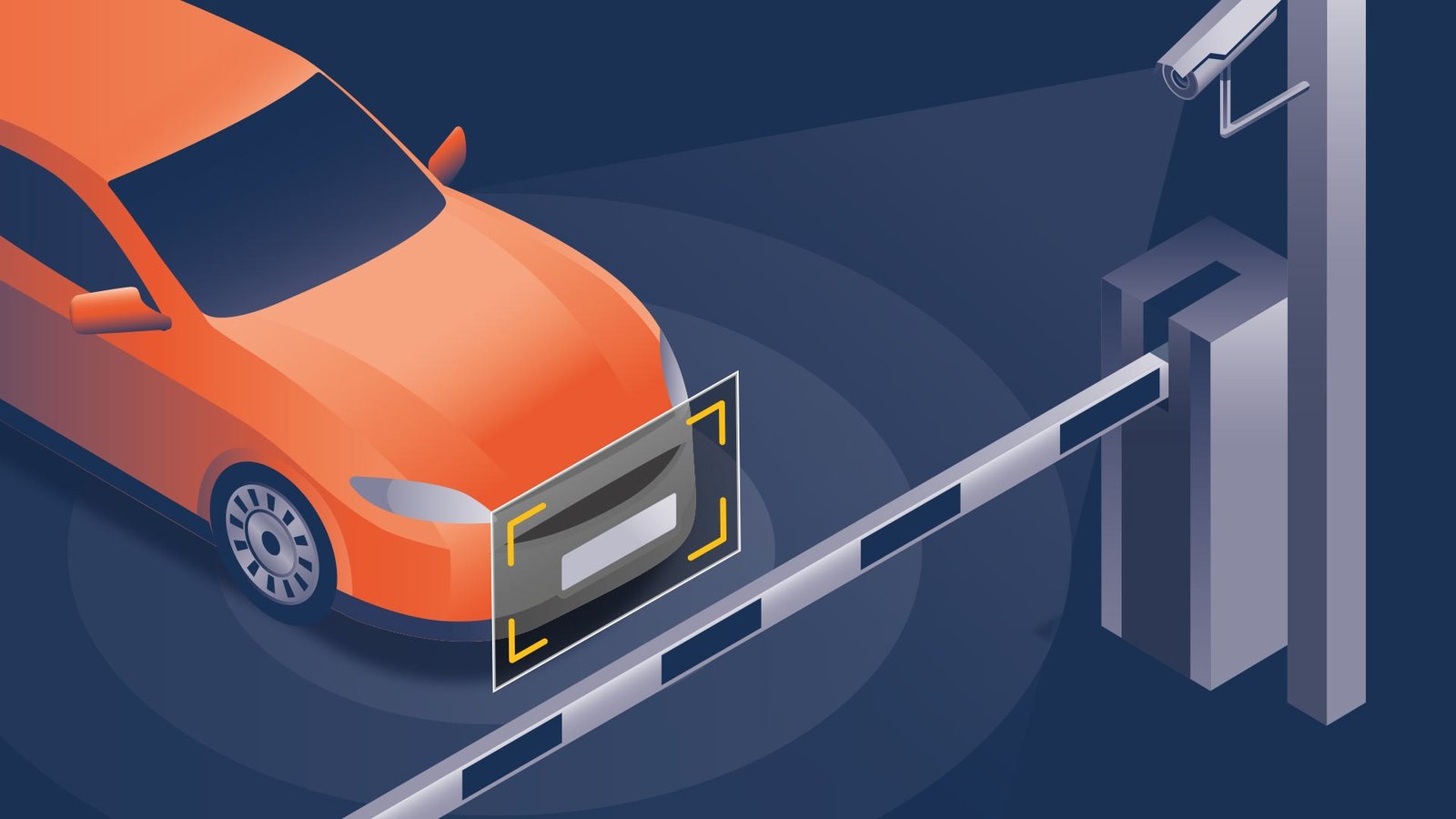
Proximity Cards: Proximity cards are physical cards that are encoded with a radio frequency identification (RFID) chip. These cards can be scanned by an access control reader, which verifies the user’s identity and grants or denies access accordingly. Proximity cards are commonly used in corporate environments, hospitals, and other facilities that require high-security measures.
Biometric Credentials: Biometric credentials are unique identifiers that use a person’s physical characteristics to verify their identity. These can include fingerprints, retinal scans, and facial recognition. Biometric credentials are highly secure and are commonly used in government facilities and high-security environments.
Smart Cards: Smart cards are similar to proximity cards, but they also contain a microprocessor that can store additional information about the user. Smart cards can be used for a variety of purposes, including access control, payment processing, and loyalty programs.
Key Fobs: Key fobs are small devices that can be attached to a keychain. These devices can be used to grant or deny access to a specific area or resource. Key fobs are commonly used in residential buildings, parking garages, and other facilities that require limited access.
BLE Bluetooth Mobile Access: Virtual card a working on mobile devices and allow its holder to open doors in premises, they are the lastest and safest technology existing for resdiential buildings, office buildings and other type of premises.

Why Are Access Control Credentials Important?
Access control credentials are a critical component of any security system. They provide an effective way to restrict access to sensitive areas or information, and they can help prevent unauthorized access to valuable assets. Access control credentials are also essential for compliance with regulatory requirements, such as HIPAA, PCI, and other security standards.
FAQs
In some cases, access control credentials can be duplicated. However, this requires specialized equipment and technical knowledge, and it’s not a common occurrence.
Yes, access control credentials can be lost or stolen. It’s important to report lost or stolen credentials immediately to prevent unauthorized access.
Yes, access control credentials can be deactivated if they are lost, stolen, or if an employee leaves the company. This is an important security measure that helps prevent unauthorized access.
Conclusion:
Access control credentials are a critical component of any security system.
They provide an effective way to restrict access to sensitive areas or information, and they can help prevent unauthorized access to valuable assets. There are several types of access control credentials, including proximity cards, biometric credentials, smart cards,